So, You’re Going to Solve the DDoS, Hacker Problem
You may have heard there was a rather big DDoS (Distributed Denial-of-Service) in the U.S. recently.
It might have even interrupted some of your video streaming, tweeting, posting. Jeezz, sorry about that.
DDoS is a lot like earthquakes here in California. There are so many all the time that unless it is really, really big; we don’t even notice them.
Don’t get me wrong, it sucks; but when you bought into the idea of connecting everything for your benefit, what did you expect?
Security and privacy are tough to get right and aren’t the first features people ask about or care about.
According to HIS Markit, folks in North America have an average of 13 internet-connected devices and CTA (Consumer Technology Association) is posting very aggressive numbers for the holiday season.
Then too, there’s the industrial or business side of the connection.
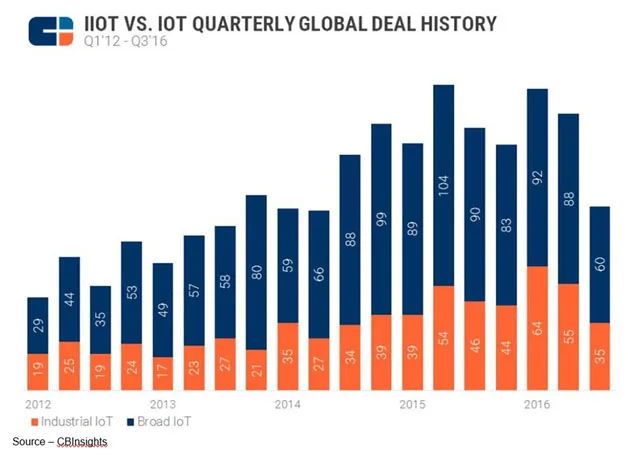
No wonder VCs (venture capitalists) are pouring money into everything in the “things” category. If you can spell IoT … they’re there, according to CB Insights.
It used to be that just computers were connected to the Internet and no one wasted time keeping software current, developing/using tough passwords, thinking twice about what they opened and backing up just in case.
Then, folks got creative about what can and should be connected to the Internet because it would let marketing use big data to sell more connectable stuff.
Connect your baby monitor so you can check on the kid when you’re in the next room, in the office, across the country. Give your little girl a Barbie that talks to her and Mattel so they can plan the next great offering.
Let your car connect to the insurance company so they can monitor your safe driving and give you a big discount. Or connect to the car company so they can tell you when you need a tune-up or oil change.
How about an intelligent thermostat that can be told to heat/cool the house because you’re coming home and want it comfortable when you arrive; or a home alarm system that opens the garage door as you approach so you don’t have to hit the button.
The music system can be connected to several streaming services and your OTT (over the top) 4K TV for even more streaming and feedback to the service so the systems can “learn” your listening/viewing taste.
Then there’s the sensor that monitors the performance of a drill press that says when it is being overused and needs a rest. Or the inventory sensor that tells shipping how many cases of soda are on hand and where they’re located so they can be quickly shipped to your grocer. It’s also automatically connected to their inventory system so they know how quickly they’re turning goods.

All your personal, home and business things have some level of security designed in to sorta’, kinda’ protect itself and provide you a degree of privacy if you read the set-up instructions and follow them … carefully.
So, you know enough to do little things like change the default username and preloaded password.
Of course, no one does that because jeezz, that stuff is boring and who wants to brag about the things’ security?
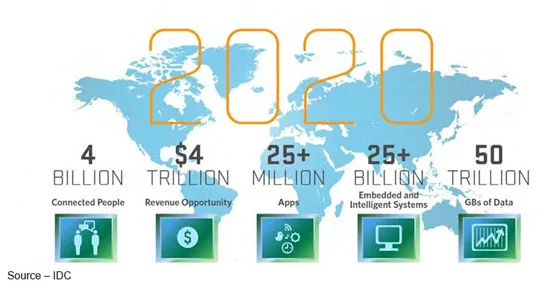
Depending on the expert you turn to, IoT is so good, so beneficial for business and individuals that more than five million new devices are being added every day.
To get their device into your business or your hands before the next guy/gal, they throw in some type of security solution, test it a couple of times and BAM! ship it so you.
In no time, they begin collecting Big Data to make your life better.

And they are constantly getting … a lot in return.
Take the minute-to-minute things you and your kids do every day:
- YouTube users upload 600 hours of video, an increase from 300 hours a year ago
- Netflix subscribers stream nearly 180,000 hours of video
- Vine users view more than 1 million videos
- BuzzFeed users watch more than 34,000 videos
- Instagram users like more than 1.7 million photos
- Snapchat users share nearly 600,000 snaps
- Pinterest pinners pin nearly 30,000 images, up from 8,400 a year ago
- Facebook users Like more than 8.1 million posts
- Twitter users tweet more than 500,000 times, up from 277,000 a year ago
- Apple users download 120,000 apps, up from 48,000 a year ago
- Amazon sees more than 10,000 unique visitors
- Uber passengers take nearly 1,000 rides
And they promise to keep your stuff private (O.K., for their own use) until some government agency comes in and asks/demands to see files; then …
While governments everywhere are demanding, that citizens have privacy with the services, sites, companies they deal with; folks only half-way agree.
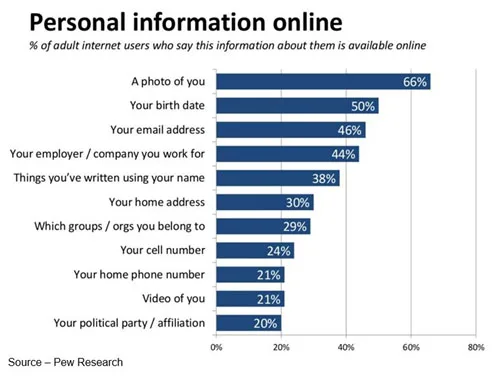
Offer them something special (discount, coupon) or say something is free if you just supply some simple information and BAM! they’ll spill their guts.
Damn, that was easy!
The problem with Dyn’s DDoS–and all intrusions–is that everyone in the food chain was part of the problem.
Duncan Brown, IDC’s research director said, “As soon as you connect something to the Internet, it’s hackable and it’s a target,”
I prefer Chambers’ comment best.
IT (information technology) folks, CSOs (chief security officers) and leading IT media have been hollering about the problem loud and clear for years.
Of course, senior management’s answer has been to put all the stuff up in the cloud, reduce the IT staff and let the cloud service worry about the issue.
Passing the buck doesn’t work for companies; IT folks know it and bet management knows it … deep down.
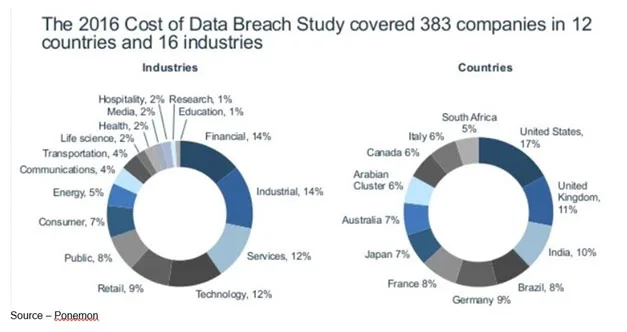
The risks are real.
And they come from a range of sources:
- Current employees
- Suppliers, business partners
- Current service providers
- Hackers and cybercriminals
It’s just as true of every connected device you buy for personal/home use.
Sure, it can cost you if someone takes control of your smartphone, home alarm system or refrigerator; but the increasingly connected car can really hurt.
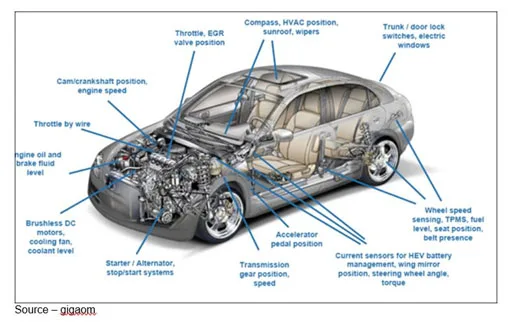
Hackers could access the car as they did with Chrysler and Jeep and cause a crash.
If they’re not that mean, they access the car through your many data points (remember, the car is constantly chatting with the manufacturer or the infotainment cloud) and hijack your personal data without you even knowing until you find out you made some weird purchases.
So?
In California terms, Dyn’s DDoS was probably only a 2.5 but it gives a hint as to what lies ahead.
Today’s Internet was never designed to be secure and robust. It’s a network of networks so more than a few have recommended the building of Internet 2.0 and do it right given today’s technical expertise and how mission critical it is for banking, health care, the power grid, etc.; and, I suppose, the other non-critical stuff like spam, email and social media posting,
Where we’d normally blame the weakest link, it seems the entire security chain is busted.
- Everything/everyone will be connected. Personal data will still be personal but easily shared/used
- To eliminate cybercrime, every person will have a personal digital identifier to ensure accurate, precise digital identity
Already a number of rulings and recommendations have been advanced by govrnments and standard groups to ensure it doesn’t happen again … yeah, right!
Yes, manufacturers must address the initial issues:
- Security/privacy must be the first design criteria, not the “oh yeah.”
- Testing must be done extensively and with a broad base of users – technically elite to luddite.
- Maintain formal advance plans on how to upgrade, enhance security when it is hacked because some kid will find a way.
- Keep detailed product records, down to the specific customer for direct contact – channel partners cannot be responsible for this burden.
Users must assume most of the responsibility in the IoT arena and that means the professional and casual customer.
The best idea I’ve heard in this area is to implement the concept that has been used in Europe for years – an identity card that contains all your information. But rather than a card, issue a personal identity code at birth and then retroactively for the rest of us.
It would be something like the DNS (domain name system) now used throughout the Internet and private networks but it would only be for the individual, not the device.
Yes, it has a gazillion drawbacks but the identity would be unique, non-transferable and identifiable for every person who goes online. There would be no memorizing complex identity codes or stupid/complex passwords or account numbers.
It may not be the solution you like, but even Pogo knows…
# # #
Comments are closed.